Blog/Article
Stop Wasting Money on Fake Traffic: How to Identify and Block It in 2026
Stop losing money on fake traffic. Learn how to identify bot traffic, detect click fraud, and block invalid visitors to protect your ads and improve conversions.
Stop losing money on fake traffic in your ads campaigns — not just “traffic,” but spend that never had a chance to convert. Every day, advertisers waste thousands of dollars on fake traffic in ads without even realizing it. Bots, click farms, and even competitors silently drain budgets. That fake traffic problem is rarely obvious in surface-level dashboards.
Learning how to block bot traffic effectively is one of the fastest ways to reduce fake traffic and improve ad performance.
In this guide, you’ll learn how to detect fake traffic, how to stop fake traffic from poisoning your funnels, and how to reduce fake traffic before it wrecks performance. We connect this to ad traffic protection and a unified traffic filtering stack (HidePages) so you can block bots from your website journeys without fragile integrations that leave footprints.
Table of Contents
- What Is Fake Traffic?
- What Is Fake Traffic (And Why It Hurts Your Ads)
- Common Sources of Bot Traffic and Invalid Clicks
- How to Detect Fake Traffic
- How to Block Bot Traffic
- Quick reference: legitimate vs suspicious traffic
- Ad Traffic Protection Strategy
- Want to Block Fake Traffic Automatically?
- FAQ
- Next steps
What Is Fake Traffic?
Fake traffic refers to visits generated by bots, scripts, or non-genuine users that do not represent real buying intent. It includes bot traffic, click fraud, scrapers, and invalid ad clicks that waste budget and distort campaign performance.
What Is Fake Traffic (And Why It Hurts Your Ads)
Fake traffic looks like real visits in your analytics but is not real demand. It often shows up as:
- Bot traffic and headless clients
- Scripted or incentivized clicks (click fraud)
- Scrapers mapping your landers and offers
- Repeated probes from invalid traffic sources (reviewers, competitors, spy stacks)
The damage goes beyond “wasted spend.” Invalid traffic poisons optimization signals. Platforms learn from conversions, time on site, and engagement. When fake traffic in ads pollutes those signals, you pay for noise and bury the angles that actually work.
Common Sources of Bot Traffic and Invalid Clicks
Fake traffic and junk clicks usually come from a few buckets:
- Click fraud and incentive traffic — Clicks for reward, not intent. Often clustered in time or geography.
- Scrapers and spy bots — They map URLs and landers; they may never “convert” but still cost money and leak intel.
- Competitors and auditors — Hard to stop with IP lists alone.
- Low-quality placements — Sometimes the placement is the problem, not your creative. Traffic filtering at the funnel still caps how much junk hits your real offer.
In 2026, fake traffic in ads is more sophisticated than ever, making detection and filtering essential.
Learning how to detect fake traffic starts with naming the bucket — prevent click fraud tactics differ from block bot traffic plays aimed at scrapers.
How to Detect Fake Traffic (Signals That Actually Matter)
You don’t need a PhD. Combine ad-platform reports with on-funnel telemetry.
Platform-side red flags
- Spikes in clicks with flat or falling real outcomes (purchases, qualified leads, deep events).
- Geo clusters that don’t match targeting or history.
- Many “visits,” almost no depth (scroll, secondary events) — pattern depends on how you measure.
On-site and server-side patterns
- Unusual data-center or headless user-agent ratios (logged responsibly and within privacy rules).
- The same funnel steps hit from a tight IP range with no progression.
- Traffic that lands on your “public” page but never acts like a warm audience.
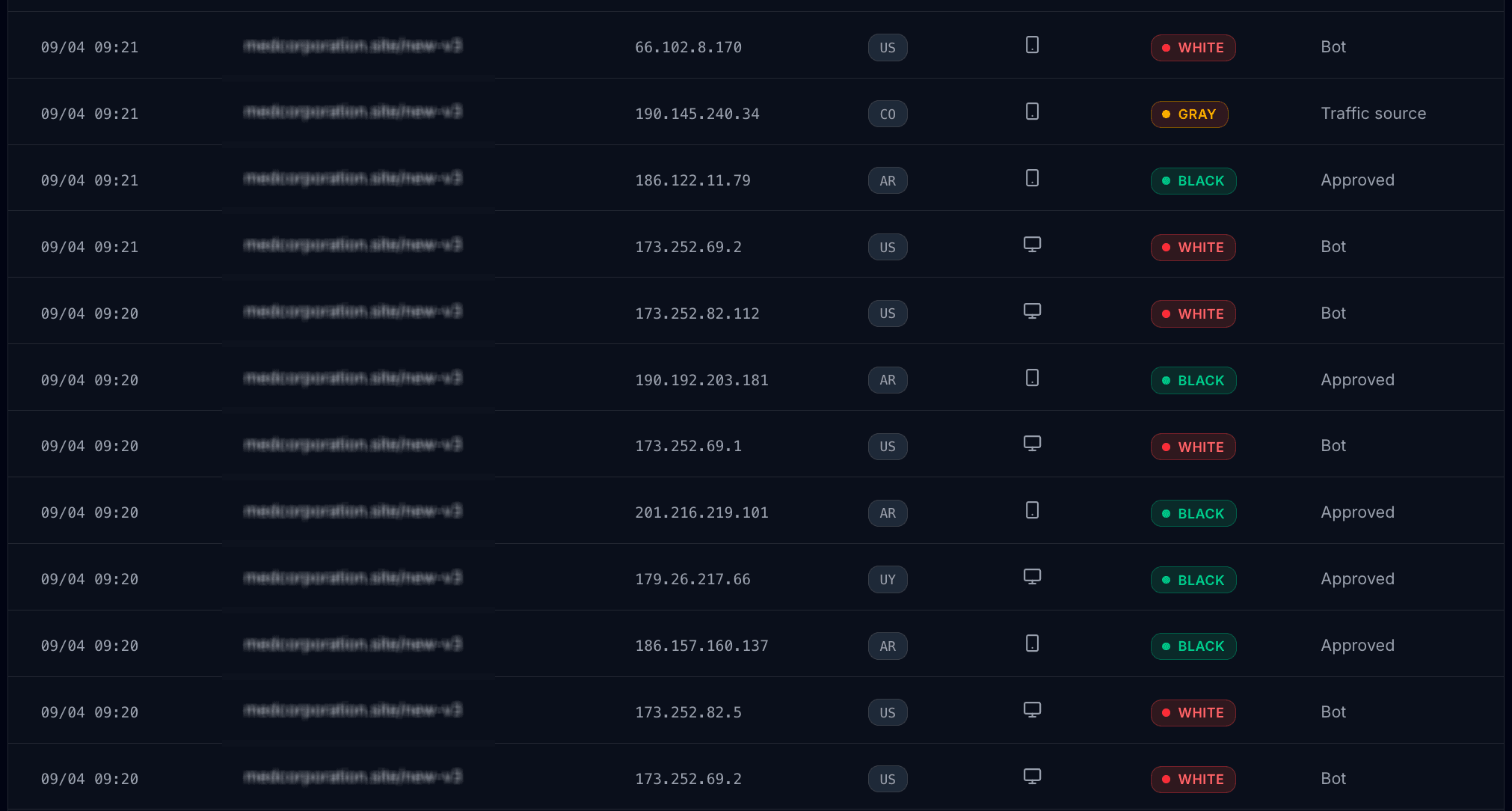
If you care about ad traffic protection, run detection as a loop: define “valid” for your offer, then measure deviation. That rule set is the core of traffic filtering.
How to Block Bot Traffic and Reduce Click Fraud
Practical stack — quick wins first, then infrastructure.
1. Tighten the Ad Layer First
- Cut placements and audiences that fail after you normalize for creative.
- Optimize for real business value, not vanity clicks — less incentive for fake clicks on ads to look “successful.”
2. Use WAF and Bot Protection
- Web application firewalls and managed bot defenses block bots from website edges — great for obvious scrapers.
- Advanced actors adapt. A WAF alone is not a full funnel-aware answer.
3. Funnel-Based Traffic Filtering
Native infrastructure wins here. Avoid generic page builders duct-taped to old cloakers. You want one environment where you:
- Create and host the pages your ads use.
- Apply filtering and routing in the same layer so each visit gets a resolution you control — not a chain of third-party hops.
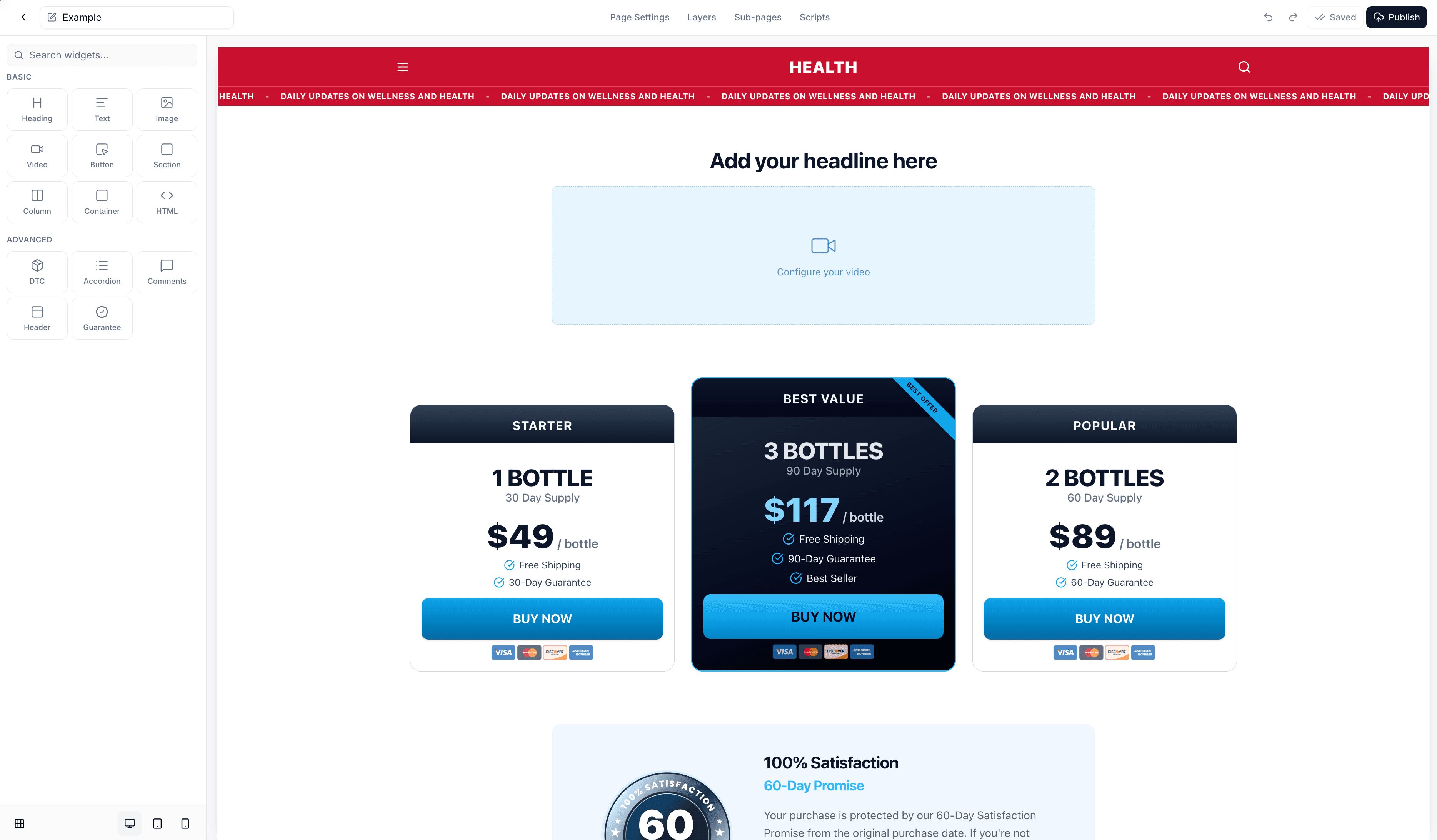
On HidePages, you block invalid traffic at the edge and decide who sees the real buyer path. Visitors that should not get your offer can be routed to a Gray Page (decoy) while your black (high-intent) experience stays isolated. That is traffic filtering as product design.
4. Zero-Redirect Routing
Legacy stacks lean on redirect chains networks and bad actors learn to fingerprint. Zero-Redirect routing (core to HidePages) cuts URL hops so the path is harder to map. To prevent click fraud and stop invalid traffic from learning your topology, fewer predictable redirects matter in 2026.
5. Monitor Traffic in Real Time
Teams scale on visibility. Live routing — timestamp, target, resolution — answers: “What did we show this visitor, and why?” Close the loop between detection and policy instead of guessing from aggregates.
If you want a deeper breakdown later, we’ll publish step-by-step guides on how to block bot traffic on the HidePages blog — useful once you’re past the checklist above.
Quick reference: legitimate vs suspicious traffic
| Signal | Often legitimate | Often suspicious |
|---|---|---|
| Click-to-conversion path | Varied timing, natural scroll / steps | Instant jumps, identical paths at scale |
| Geography | Matches targeting & history | Dense bursts from odd regions |
| Repeat visits | Some returning research behavior | Same IPs hitting funnel edges on loop |
| User agent / client | Common browsers | Headless, empty, or datacenter-heavy patterns |
| Post-click behavior | Engages with your real offer flow | Stalls on surface pages, never deepens |
Use this when you audit bot traffic — not as a verdict on every single visit.
Ad Traffic Protection Strategy for 2026
Fake traffic and click fraud keep evolving. Strong teams treat invalid traffic as infrastructure:
- Detect — clear definitions plus ad-platform and on-funnel signals.
- Block — obvious bot traffic; fewer fake clicks on ads via placement hygiene and edge tools.
- Route — a filtering layer that matches your risk model, including decoys for hostile automation.
Prefer native stacks: pages + hosting + traffic filtering + routing in one place. Patchwork is where leaks show up — what HidePages was built to replace.
Want to Block Fake Traffic Automatically?
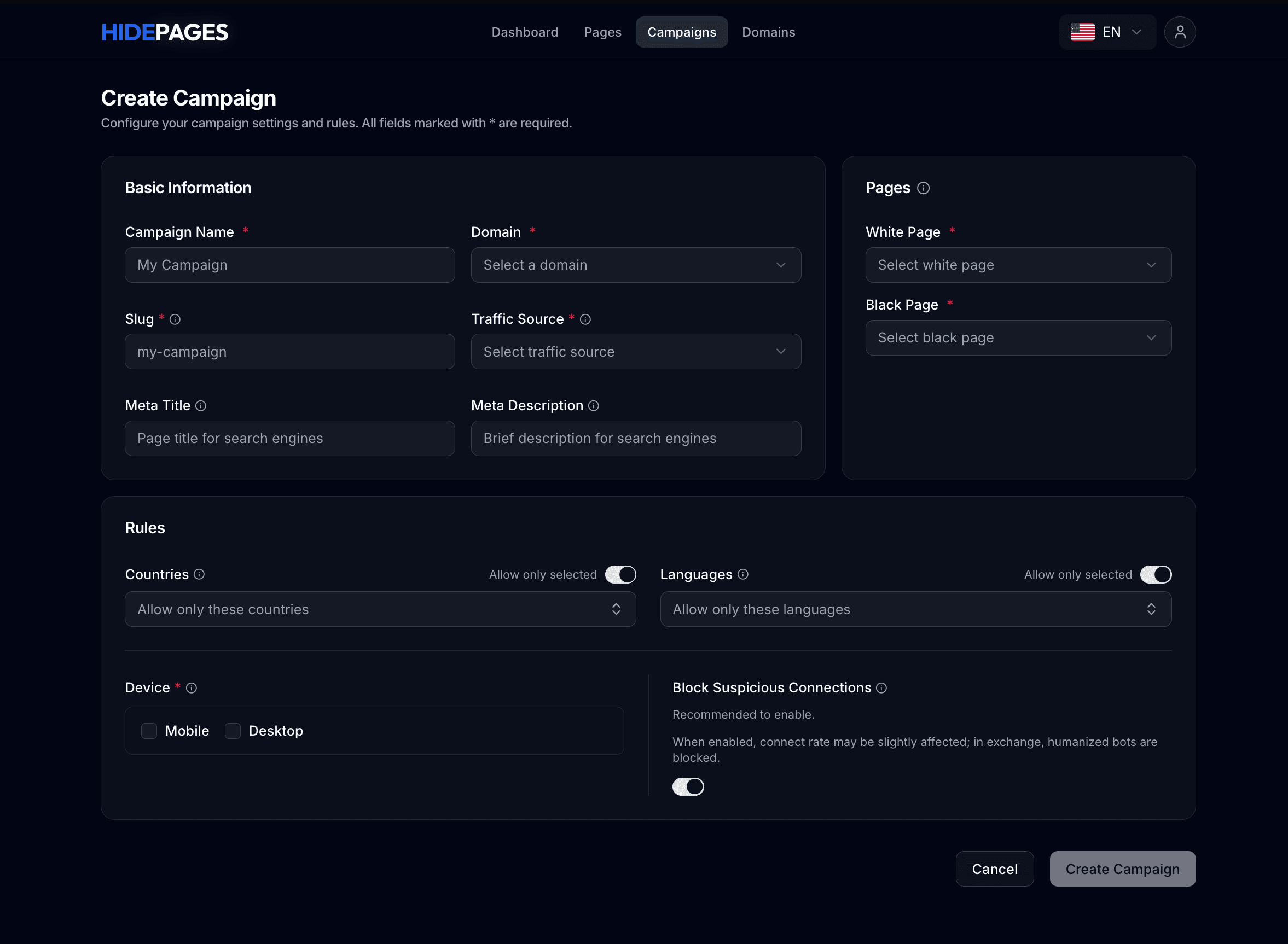
If you’re serious about protecting spend, a traffic filtering platform like HidePages helps you:
- Block bot traffic in real time
- Filter by country, device, language, and behavior
- Route suspicious visitors away from your real funnel
You stop guessing and control who sees your offers.
At the end of the day, fake traffic is not just a nuisance — it's a silent profit killer.
Get started with HidePages and start reducing fake traffic on your campaigns today.
FAQ
Next steps
Map one campaign’s “valid visitor” profile this week. Pick three measurable signals tomorrow. Align your stack so those signals drive who sees what — that’s how you stop fake traffic from hiding inside “good” dashboards. For more on building protected funnels, browse the HidePages blog.